Nmap cheat sheet: From discovery to exploits, Part 3: Gathering additional information about host and network | Infosec Resources

Nmap cheat sheet: From discovery to exploits, Part 3: Gathering additional information about host and network | Infosec Resources




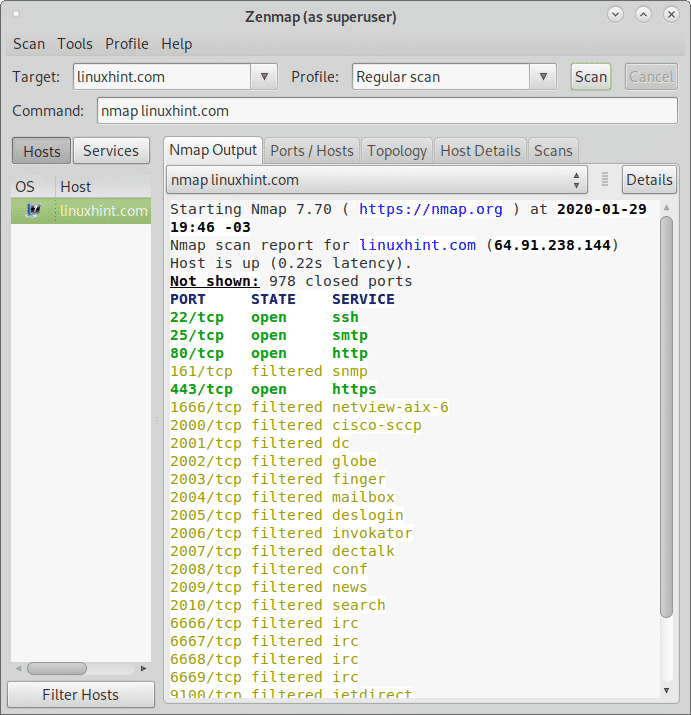
![Lesson 8]Network Vulnerability and Scanning: Operating System Detection in Nmap | Medium Lesson 8]Network Vulnerability and Scanning: Operating System Detection in Nmap | Medium](https://miro.medium.com/max/1320/1*olIHpP0rpyJ6TW12EQUFng.png)






![Lesson 8]Network Vulnerability and Scanning: Operating System Detection in Nmap | Medium Lesson 8]Network Vulnerability and Scanning: Operating System Detection in Nmap | Medium](https://miro.medium.com/max/1400/1*UxyqoqMltXme2yxFc_OPeQ.png)